Network Security Interview Questions and Answers 2023
Network Security is a vast and comprehensive field that provides threat protection to your network and data via hardware or software solutions, processes, protocols and configurations. It involves access control, application security, virus and antivirus software, network analytics, encryption and more.
In today’s digital world, organisations, whether large or small, use both internal and external networks. Generally, networks share information via the internet which makes them vulnerable to attacks and hacks. These cyberattacks can adversely affect a company’s business operations and hence its reputation. Therefore, securing these computer networks is crucial for the company’s successful functioning.
This gives rise to ample opportunities for cybersecurity experts. Therefore, in this article, we will be focusing on commonly asked networking questions for interviews.
1. What are the possible consequences of an attack on a computer network?
2. In the context of network security, what do you understand by vulnerability, threat, and risk?
3. What type of home network do you use? How do you protect it?
4. What is meant by a network security firewall, IDS, and IPS?
5. What are some of the common network security threats?
6. What is the difference between VLAN and VPN?
7. What are SSL and TLS?
8. Can you recall the latest network security breach? From where did you learn about it?
9. What defence will you use against the following attacks: brute force attack and man-in-the-middle attack.
10. What is the CIA triad?
11. Explain handshake in network security.
12. How do you set up a network security firewall?
13. Explain the OSI Model in network security.
14. What is the Address Resolution Protocol? How does it work?
15. What is a salted hash technique?
1. What are the possible consequences of an attack on a computer network?
A cybersecurity attack on your organisation can significantly impact your business. A security breach can cause damage particularly in three areas: economic, reputational and legal.
The organisation can suffer economic damage due to the following:
- Theft of corporate information
- Theft of financial data
- Disruption of trading
- Loss of business or contract
- Cost in repairing affected networks and systems
A network attack damages the company’s reputation and erodes the client’s trust in you. This results in:
- Loss of customers
- Loss of sales
- Reduced profits
- Impacted relationship with stakeholders
Apart from financial and reputational damage, a cyberattack can also have legal consequences. Any compromise in personal and sensitive data, whether accidental or deliberate, violates data protection and privacy laws. And if you do not deploy appropriate security measures, you might have to pay hefty fines and regulatory sanctions.
2. In the context of network security, what do you understand by vulnerability, threat, and risk?
Vulnerability: A weakness in hardware, software, procedures or personnel, that hackers or threat actors can exploit to achieve their goals is known as a vulnerability.
Examples of vulnerability include a publicly exposed networking device, a buffer overflow in a browser, or even a disgruntled employee susceptible to phishing attacks.
The process of discovering, reporting and fixing security vulnerabilities is known as vulnerability management.
Threat: A threat refers to any type of danger or a potential cyberattack that can damage a network, steal data, create a disruption in the functioning of the network, or cause any harm in general. Few examples of threats are malware, phishing, data breaches, etc.
Gaining information about a threat and its actors is known as threat intelligence.
Risk: It is a combination of the probability of a threat occurrence and the impact a vulnerability can cause. The below formula represents the same:
Risk = Threat Probability * Vulnerability Impact
The process of identifying, assessing and controlling risks or threats to the confidentiality, integrity, and availability of a company’s data and network is known as risk management.
3. What type of home network do you use? How do you protect it?
The interviewer will gauge how you put your network security skills to use in everyday life. The measures that you use to secure your home network says a lot about your savviness in this field.
First, mention the home network you use, whether wireless or Ethernet.
Then based on your type of network, speak about the methods that you use for their security.
For a wireless network, some points worth mentioning are:
- Enabling network encryption like WAP2.
- Changing the default SSID(service set identifier)
- Disabling SSID broadcasting
- Frequently updating routing software
- Turning the firewall on
Also include some points for wired network security:
- Keeping the network up-to-date
- Performing audit and mapping
- Including MAC address filtering
- Using 802.1x protocol for authentication
- Encrypting the entire network
4. What is meant by a network security firewall, IDS, and IPS?
Firewall: A network security firewall is a system that acts as a barrier between a trusted network and the outside network or systems. A firewall filters and monitors the incoming and outgoing network traffic according to pre-established security policies. You can create a firewall through software, hardware or a combination of both.
IDS or Intrusion Detection System: An IDS is a passive system that analyses the data packets traversing a network, checks the signature patterns for anomalies and compares them with known signatures of cyberattacks. In case of detection of a potential threat, the IDS raises a red flag and the concerned person or authority needs to act on it.
IPS or Intrusion Prevention System: IPS also analyzes the data packets but instead of raising an alarm, it actively blocks the packet that is a threat to the network. Therefore, an IPS helps in stopping the attack altogether.
5. What are some of the common network security threats?
Apart from computer virus and trojan horse, below are some other commonly occurring network security threats:
- Malware
- Phishing
- Password attacks
- Denial of Service attack (DoS)
- Distributed Denial of Service attack(DDoS)
- SQL Injection
- Man in the middle attack
- Drive-by downloads
- Malvertising
- Rogue software
- Brute force attack
6. What is the difference between VLAN and VPN?
| VLAN (Virtual Local Area Network) | VPN |
| It is a subcategory of VPN and is used by organisations to group devices that are distributed across several locations | Used to create a secure network connection between two different locations, owned by a single entity. For example, two offices of the same company. |
| Ideal for managing a network by splitting it, but does not offer many security features. | More secure as it provides encryption and anonymization. |
| VLAN is cost-efficient as it reduces the need for routers and the expenses related to their installation. | VPN’s are costlier to implement owing to their advanced security features. |
7. What are SSL and TLS?
SSL or Secure Socket Layer: It is a technology to secure any data transmission between two networks by encrypting sensitive information. The two networks can be either client and server, like an eCommerce site and a web browser, or a server to server network, for example, a server containing employee’s personal details communicating with the payroll server.
TLS or Transport Layer Security: It is an updated and more secure version of the SSL and offers a secure channel between two networks through data security and privacy.
8. Can you recall the latest network security breach? From where did you learn about it?
Network security is a volatile field with new cyberattacks making the headlines every other day. In recent years, there have been several high-profile data and network breaches as hackers come up with new and innovative ways to attack. And the interviewer would want to know how you keep yourself up-to-date with such information.
As a hotshot network security engineer, you must be well-versed in all such cyberattacks and the vulnerabilities that led to the breach. If not already, you must make it a practice to keep yourself well-informed with the latest news and incidents related to network security.
Some ways to stay informed are:
- Follow a well-known network security professional
- Browse through the current security trends
- Attend live network security events
- Listen to podcasts
- Follow blogs and/or newsletters
9. What defence will you use against the following attacks: brute force attack and man-in-the-middle attack.
Brute force attacks happen when a hacker or unauthorised personnel take infinite attempts to crack a password.
Here are 5 possible ways to defend against this attack:
- Account lockout: When multiple incorrect passwords are entered into an account, it is locked or temporarily suspended and can only be opened by an administrator.
- Progressive delay defence: An offending account is locked for ‘X’ number of days after someone makes ‘Y’ unsuccessful login attempts.
- Challenge-response authentication: After a few unsuccessful password attempts, a question is asked whose answer will be known to only an authorised user.
- Captcha: It is used to make an attack by automated bots ineffective.
- Two Factor Authentication (2FA): Because password alone is not sufficient to prevent attacks, the second level of authentication is brought in. For example, a security code is sent to your mobile or email.
A Man in the Middle attack takes place when an eavesdropper monitors and controls a conversation between two links in a network. The users at the receiving end are completely unaware of the situation.
You can prevent man-in-the-middle attack through following ways:
- Stay away from public networks and open Wi-Fi networks
- Secure your emails by employing TLS/SSL on the server
- Use VPN to create a secure connection from your organisation
- Keep the browsers updated with the latest security features
10. What is the CIA triad?
CIA triad is a widely used model designed to guide organisations with Information Security related policies and help them keep their network and data safe.
The initials of CIA stands for the three pillars of cybersecurity: Confidentiality, Integrity, and Availability.
Confidentiality
This pillar is about ensuring that no private and sensitive information is subjected to unauthorised access. Only authorized persons are allowed to access the data.
The common means to manage confidentiality is access control lists, Unix file permissions, and data encryption.
Integrity
Integrity ensures that there has been no modification in the data by an unauthorised entity. And in case an authorized modification in data was unsuccessful then integrity also makes certain that the data is reversed back to its original state without being corrupted.
Availability
The final component of the CIA triad is to make sure that the data is available to the authorised users whenever they request it. High availability can be maintained by the latest hardware and software updates and regular data backups and recovery.
11. Explain handshake in network security.
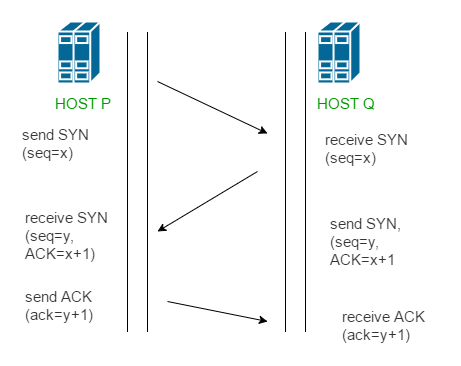
Handshaking is a process that connects two devices in the network for communication. To establish the communication, it requires the client and server to negotiate SYN (synchronization) and ACK (acknowledgement) packets. For instance, if two devices are connecting through a router or a modem, then the handshaking determines the protocols, compression methods, transmission speed and error-correction methods, etc. to be used during the communication session.
There are two types of handshakes:
- Two-way handshake: It’s a two-step process with the exchange of SYN and ACK packets.
- Three-way handshake: Three-step process with SYN, SYN+ACK, and ACK packets being exchanged. This is shown below:
12. How do you set up a network security firewall?
Follow the below steps to set up a firewall:
- Change the default password for the firewall device.
- Disable the remote administration feature.
- Certain applications may require port forwardings like web and FTP servers. Configure port forwarding for all such applications so they continue to work properly.
- Disable the firewall’s dynamic host configuration protocol (DHCP), else installing the firewall will create a conflict if the host machine has an existing DHCP.
- Logging should be enabled and you should know how to view logs to check for any firewall issues or potential attacks.
- Configure the network security firewall to enforce strong security policies.
13. Explain the OSI Model in network security.
An OSI (Open System Interconnection) model is a reference model for enabling communication between applications over a network. It acts as a guide for developers and vendors for creating software applications and digital communication products that can interoperate efficiently.
The OSI Model consists of seven layers:
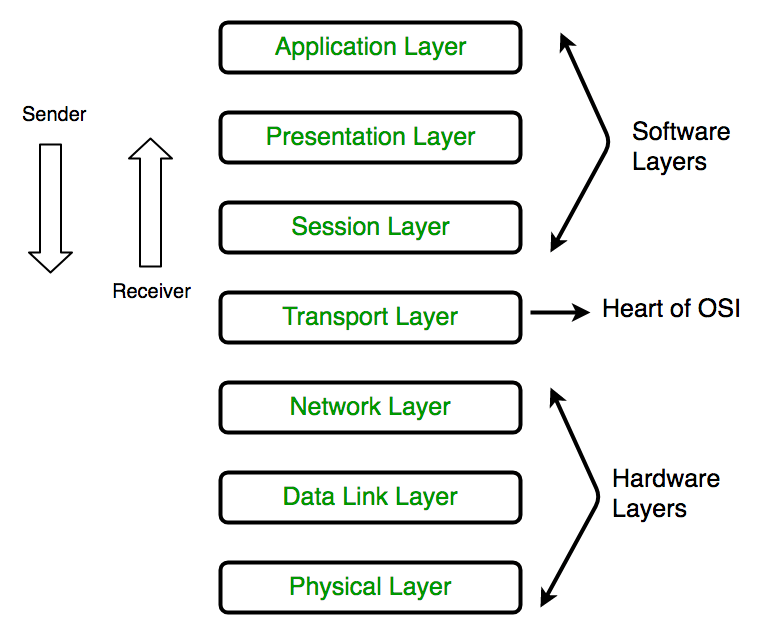
- Physical Layer: This layer is responsible for creating a wired or wireless connection for the transmission of data between two nodes in a network. The transmission and reception of data are in raw bitstreams i.e. in a string of 0’s and 1’s.
- Data Link Layer: Node to node data transfer between directly connected network nodes. It divides the data packets into frames and transmits them from the source node to the destination node. It also corrects any error that may have occurred at the physical layer. It consists of two sub-layers:
- MAC(Media Access Control): Multiplexing for physical device transmission.
- LLC(Logical Link Control): Responsible for the flow of data and error control.
- Network Layer: It is responsible for two functions:
- Takes frames from the data link layer and segments them into network packets for transmission and then reassembling them at the receiving node. It uses the IP address mentioned in the frame to identify the receiving node.
- Routing network based on IP address and finding the shortest path across a physical network.
- Transport Layer: Responsible for data packet delivery and error checking. It regulates the packet size, sequence and performs end to end communication using Transmission Control Protocol(TCP).
- Session Layer: Creates sessions and controls the connection between different systems in a network. It is responsible for setting up, managing and terminating the session between different nodes. It also includes synchronisation, authentications and reconnections.
- Presentation Layer: Formats and translates data for the application layer according to the semantics accepted by the application. It can also take care of the encryption and decryption requirements of the application layer.
- Application Layer: Both the application layer and the end-user interact directly with the application at this layer which focuses on process-to-process communication. This layer also synchronizes the communication, identifies communication partners, and checks resource availability.
14. What is the Address Resolution Protocol? How does it work?
Generally, computer applications use IP (Internet Protocol)addresses or logical addresses to transmit and receive messages. But the actual communication between two applications or systems takes place through physical or MAC (Media Access Control) addresses. Therefore, a protocol is needed to map the logical address to a physical address and get the endpoint MAC address. This protocol which translates IP addresses to MAC addresses is known as Address Resolution Protocol or ARP.
How ARP works:
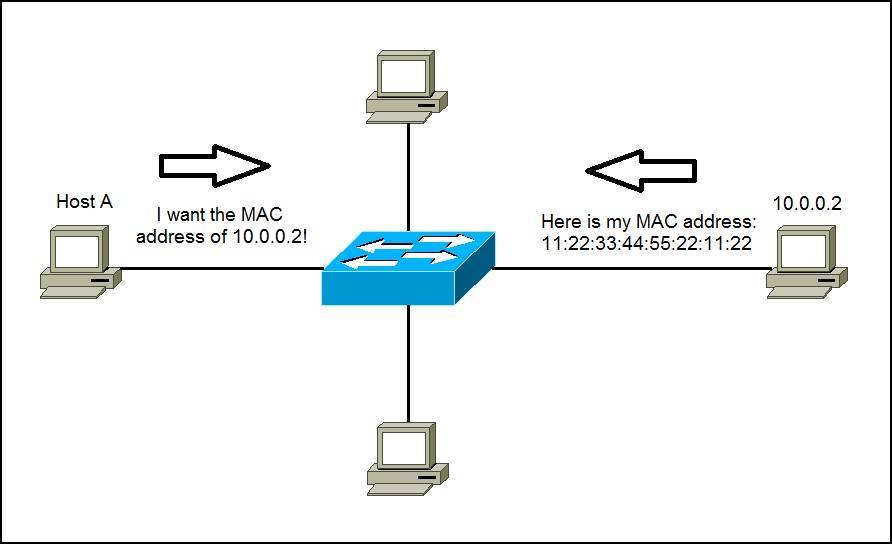
Every computer in a Local Network Network(LAN) has an associated IP address for unique identification and communication.
If a system or a device wants to communicate with another system over the internet, then it broadcasts an ARP request packet to all the machines in its network.
The devices in the network remove the header from this data packet and transfer the packet to the network layer. This layer then validates the network ID of the packet with its destination IP’s network ID. If the two IDs are equal, then the source receives an ARO response enclosing the MAC address of the destination. Otherwise, the packet reaches the network gateway and is broadcasted to the rest of the machines it is connected with.
The above process continues until an ARP response is sent back with the destination MAC address.
15. What is a salted hash technique?
A salted hash is a transmission technique for passwords to make them stronger. This is done through a process called salting wherein the password is hashed with some special characters. This increases the password strength as it is now lengthy that too with a random set of characters making it difficult for hackers to crack it.
Cybersecurity covers a wide range of topics and you would want to cover as much as possible before facing the interviewer. This post on networking questions for interviews would have given you a good idea of what to expect during your interview. Additionally, do visit our post on ethical hacking to gain general information on cybersecurity.
Apart from going through the essential topics, be ready to demonstrate your passion for the role and practice a lot to perfect your responses.
Backend Technology Interview Questions
C Programming Language Interview Questions | PHP Interview Questions | .NET Core Interview Questions | NumPy Interview Questions | API Interview Questions | FastAPI Python Web Framework | Java Exception Handling Interview Questions | OOPs Interview Questions and Answers | Java Collections Interview Questions | System Design Interview Questions | Data Structure Concepts | Node.js Interview Questions | Django Interview Questions | React Interview Questions | Microservices Interview Questions | Key Backend Development Skills | Data Science Interview Questions | Python Interview Questions | Java Spring Framework Interview Questions | Spring Boot Interview Questions.
Frontend Technology Interview Questions
HTML Interview Questions | Angular Interview Questions | JavaScript Interview Questions | CSS Interview Questions
Database Interview Questions
SQL Interview Questions | PostgreSQL Interview Questions | MongoDB Interview Questions | MySQL Interview Questions | DBMS Interview Questions
Cloud Interview Questions
AWS Lambda Interview Questions | Azure Interview Questions | Cloud Computing Interview Questions | AWS Interview Questions
Quality Assurance Interview Questions
Moving from Manual Testing to Automated Testing | Selenium Interview Questions | Automation Testing Interview Questions
DevOps and Cyber Security Interview Questions
DevOps Interview Questions | How to Prevent Cyber Security Attacks | Guide to Ethical Hacking
Design Product Interview Questions
Product Manager Interview Questions | UX Designer Interview Questions
Interview Preparation Tips
Strength and Weakness Interview Questions | I Accepted a Job Offer But Got Another Interview | Preparation Tips For the Virtual Technical Interview | 7 Tips to Improve Your GitHub Profile to Land a Job | Software Engineer Career Opportunities in Singapore | What can you expect during a whiteboard interview | How To Write A Resignation Letter | Recommendation Letter Templates and Tips.
Quick Links
Practice Skills | Best Tech Recruitment Agency in Singapore, India | Graduate Hiring | HackerTrail Litmus | Scout - Sourcing Top Tech Talent in ONE Minute | About HackerTrail | Careers | Job Openings.